新聞中心
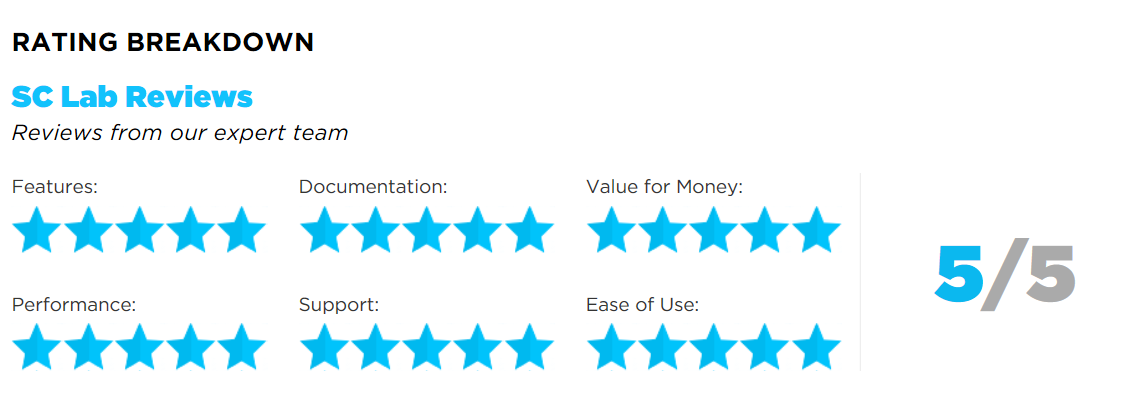
SC雜誌評論搶先看
Sophos端點優勢 : 容易使用,優越的技術支援並能恢復被勒索加密的檔案。
Sophos端點缺點 : 我們沒看到任何缺點。
SC雜誌定論 : 這是個完善的防勒索工具,價格剛好且技術支援不錯,的確值得關注,這是我們這個月主推的多功能產品。
SC雜誌評論請參閱以下英文報導,您也可至SC雜誌官網參閱完整原文報導,
網址 https://www.scmagazine.com/sophos-intercept-x-and-endpoint-protection/review/9340/
SUMMARY
Of the products examined this month, this one had the easiest start-up. It also clearly showed its anti-malware pedigree. One of the things that has plagued us recently is what we consider substandard documentation. When we have difficulty deploying a product under test, we naturally turn to the documentation for guidance. Often that guidance is not forthcoming. First, we had no difficulty deploying in this case, but if we had we would have found the quick-start guide more than adequate.
This is an Attack Phase tool but it has overtones of phase three, Cleanup, in one of the nicest functions we've seen. We tested it with both Locky and Satan RaaS. Prior to attempting to detonate the ransomware samples in a protected environment, we detonated each on in an unprotected virtual machine. We had to play a couple of tricks on Satan to get to ignore that it was in a virtual machine. In each case, encryption of several thousand files took just seconds. We reverted the machines and applied the Sophos tools.
We saw no indication that either sample had detonated successfully. If, however, it had, the tool catches the attempted encryption, saves a copy of the target file and when everything is over and the malware is gone, it restores the saved copy. It's a sort of on-demand backup on a file-by-file basis with the ransomware making the demand by virtue of trying to encrypt the file.
The Intercept X product adds this functionality on top of any vendor's anti-malware product. We have observed Windows Defender responding slowly to certain types of malware, including ransomware in the lab. For many types of malware, that poses no great difficulty, but in a ransomware attack it can be disastrous since within two minutes or less the damage is done. The addition of Intercept X can mitigate that problem.
Additionally, we liked the root cause analysis. This is very graphical but with very good drill-down that gives you a clear view of what happened during an attack. Cleanup of the malware itself is, as one would expect, automatic.
Pricing for this tool is quite reasonable and given that enhanced 24/7 support is included at no extra cost, this is a very good value. In the matter of support, we usually are interested when "enhanced support" is available at no extra cost. In this case, it's the real deal. That said, under most circumstances we can't see a lot of need for support given simple deployment and straightforward operation.
However, there are occasional issues and the support section of the website has a large and vocal community. For example, one user reported that he had tested Intercept X with a simulator from a competitor and it appeared that CryptoGuard - the active tool in Intercept X - didn't stop the simulator. In fact it did, but the simulator reported it wrong. Sophos, of course, reported the fault to the other vendor.
In addition to the community questions, there is a blog, forums, a file download area and a knowledgebase. With all of this functionality readily at hand, calling support should be only rarely necessary.
Documentation is first-rate and, overall, we really liked this product and the results it produces.







